AI-powered endpoint monitoring is reshaping cybersecurity by detecting and stopping threats in real time. Unlike older methods that rely on known malware signatures, AI tools focus on behavior patterns to identify unusual activity, making them effective against zero-day attacks and advanced threats.
Key Takeaways:
- Why It Matters: 70% of cyber breaches originate from endpoint devices, and traditional antivirus struggles to keep up with modern threats.
- How It Works: AI tools monitor behavior, learn normal patterns, and flag anomalies like unusual user activity or file access.
- Benefits:
- Reduces response time from hours to minutes.
- Automates threat detection and remediation, saving IT teams over 40 hours weekly.
- Cuts costs by preventing breaches, which can average $3.3 million per incident.
- For SMBs: Affordable solutions ($30–Affordable solutions ($30–$100 per endpoint annually) help smaller businesses access enterprise-level protection.00 per endpoint annually) help smaller businesses integrate AI to access enterprise-level protection.
AI endpoint tools also integrate across devices and platforms, offering centralized management and compliance reporting. This makes them ideal for businesses managing hybrid or remote workforces. Endpoints are now the frontline of cybersecurity, and AI is proving to be a game-changer in protecting them.
Endpoint security in the AI era: What's new in Defender | BRK240
sbb-itb-bec6a7e
How AI Improves Real-Time Threat Detection
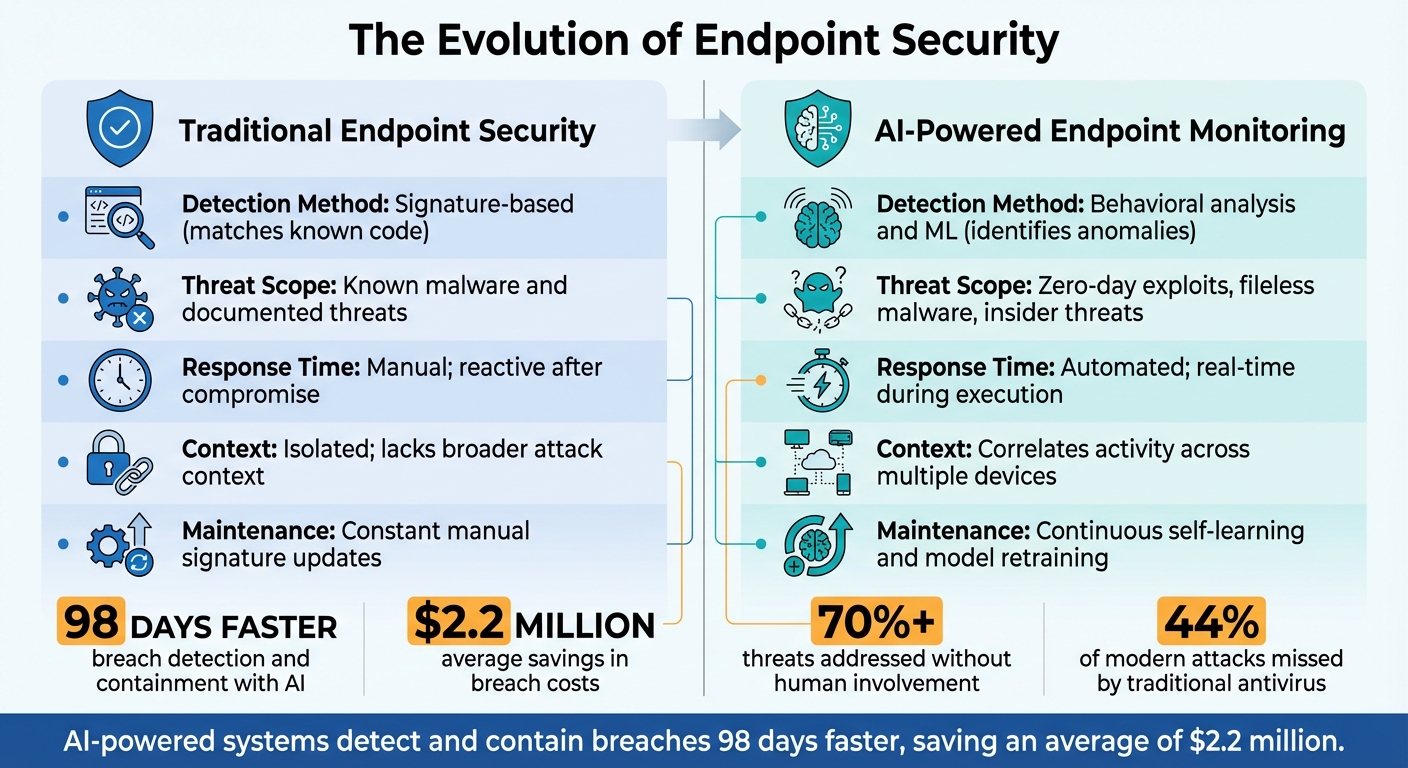
Traditional vs AI-Powered Endpoint Security Comparison
AI is reshaping endpoint security by monitoring behavior around the clock to quickly spot anomalies. Traditional systems often rely on static threat databases, which can leave gaps in coverage. In contrast, AI-driven systems continuously learn and adapt to behavioral patterns. These systems track how processes run, how files are modified, and how network traffic behaves. If something deviates from the usual - like a PowerShell script running at 3 a.m. or a user suddenly accessing hundreds of files - the system flags it right away.
Machine Learning for Threat Detection
Machine learning models take 2 to 4 weeks to observe and establish a baseline for normal behavior within your environment. During this time, the AI analyzes patterns such as user logins, application usage, and network traffic. Once trained, the system uses four detection layers: signature scanning for known threats, behavioral classification to spot ransomware variations, unsupervised anomaly detection for zero-day exploits, and pre-execution analysis to catch fileless attacks that operate in system memory instead of on disk.
Supervised models rely on labeled datasets to recognize known threats and their variations. Meanwhile, unsupervised models detect new, unknown attacks by identifying statistical outliers - activities that stand out as suspicious even if they’ve never been seen before. This dual-layered approach allows AI to tackle both evolved versions of existing malware and entirely new attack types. Additionally, the system correlates suspicious activities across devices, uncovering coordinated attack patterns that human analysts might overlook when only examining single alerts.
"Traditional antivirus and rule-based tools can't keep up with today's stealthy techniques. AI-powered Endpoint Detection and Response (EDR) changes this by using behavioral analytics, machine learning, and automation to detect and stop threats in real time." - Hannah Bennett, BitLyft
Automated Response and Speed
Once threats are identified using machine learning, speed becomes critical. Attackers can escalate from the initial breach to deeper network access in just 48 minutes. AI-powered systems act instantly, isolating compromised devices, stopping malicious processes, and reversing unauthorized changes without waiting for human intervention. Organizations that rely heavily on AI automation detect and contain breaches 98 days faster than those using manual methods, saving an average of $2.2 million in breach-related costs.
In fact, automated remediation addresses over 70% of threats without human involvement, reducing response times from hours to mere minutes. For example, when E INC, a software company serving automotive dealers, implemented SentinelOne's AI-driven endpoint security, the system autonomously detected and blocked threats in real time. This allowed the company to maintain robust security without needing to build a large internal Security Operations Center. By shifting from reactive to proactive defense, these systems neutralize threats during execution, preventing damage before it occurs. This seamless integration of detection and automated response sets the stage for the business advantages covered in later sections.
| Feature | Traditional Endpoint Security | AI-Powered Endpoint Monitoring |
|---|---|---|
| Detection Method | Signature-based (matches known code) | Behavioral analysis and ML (identifies anomalies) |
| Threat Scope | Known malware and documented threats | Zero-day exploits, fileless malware, insider threats |
| Response Time | Manual; reactive after compromise | Automated; real-time during execution |
| Context | Isolated; lacks broader attack context | Correlates activity across multiple devices |
| Maintenance | Constant manual signature updates | Continuous self-learning and model retraining |
Key Features to Look For
With endpoints responsible for nearly 70% of breaches, it's crucial to select tools that offer strong behavioral analysis, automated responses, and smooth integration with your existing systems.
Real-Time Monitoring and Alerts
Continuous behavioral monitoring is the backbone of effective endpoint security. AI systems create a baseline of "normal" activity for each user and device, tracking things like logins, file access, and application usage. If something unusual occurs - like a user accessing sensitive files from an unexpected location or a PowerShell script running at an odd hour - the system flags it immediately.
This proactive approach is particularly effective against attacks leveraging native tools like PowerShell or Windows Management Instrumentation (WMI), which traditional signature-based tools often overlook. Instead of waiting for damage to unfold, these systems act instantly. High-risk activities can trigger automated responses such as isolating a device, terminating a malicious process, or blocking network access - often in milliseconds - to stop threats from spreading across your network. This kind of automation enhances security without increasing the workload for your team.
"Most ransomware attacks begin on endpoints and show detectable behavioral signals before encryption starts." - BitLyft
In addition to real-time alerts, integrating these tools across platforms ensures complete coverage of your devices.
Cross-Platform Integration
Chances are, your organization uses a mix of Windows laptops, macOS devices, Linux servers, and mobile phones - some of which may be personal devices under BYOD policies. Cross-platform compatibility ensures visibility across all these endpoints. Without it, gaps in monitoring can become hiding spots for threats.
A unified "single-pane-of-glass" dashboard consolidates data from all devices, eliminating the inefficiency of juggling multiple tools. This centralized approach allows you to enforce security policies - like encryption, access controls, and updates - consistently across devices, no matter their type or location. For smaller teams with limited IT resources, this streamlined management is a game-changer. Integration with existing tools, such as SIEM or XDR systems, further enhances threat detection and speeds up incident resolution.
"The endpoint is where AI operates, and the interaction layer is where risk emerges, so without local sensors that understand AI context and behavior in real time, security teams are making decisions without the visibility they need." - Lior Drihem, Prompt Security
Once integrated, the data collected becomes a powerful tool for generating actionable insights.
AI-Generated Insights and Reports
Raw data alone isn’t very helpful. AI systems sift through the noise, transforming thousands of daily events into actionable intelligence. Instead of bombarding your team with low-priority alerts, automated triage highlights the most critical incidents, reducing alert fatigue and letting your staff focus on what truly matters.
AI also examines historical data to identify patterns and assess risks. These predictive insights help you address potential vulnerabilities before attackers can exploit them. For organizations in regulated industries, AI-driven reporting simplifies compliance by logging events and generating documentation to meet standards like GDPR, HIPAA, and PCI-DSS.
| Feature | Practical Value for SMEs |
|---|---|
| Automated Remediation | Automatically stops attacks, reducing the need for constant manual monitoring |
| Single Pane of Glass | Centralizes data management, making it easier for small teams to oversee multiple devices |
| Scalability | Enables small IT teams to manage more devices without additional staff |
| Compliance Reporting | Automatically generates reports for regulations like HIPAA, GDPR, or SOC 2 |
| Behavioral Baselines | Detects phishing and social engineering attempts by flagging unusual user behavior |
Benefits for Businesses
Better Security and Threat Prevention
AI-powered endpoint monitoring offers a stronger defense against cyberattacks than traditional antivirus software. With around 90% of successful cyberattacks and 70% of data breaches starting at endpoint devices, securing these access points is crucial. Organizations using AI-driven endpoint detection and response (EDR) experience 60% to 85% fewer successful attacks compared to those relying on older methods. This technology excels at detecting advanced techniques, such as "living-off-the-land" attacks, where hackers exploit legitimate tools like PowerShell to avoid detection. By creating behavioral baselines and flagging unusual activity immediately, AI can uncover hidden threats before they cause significant damage. These advanced defenses help businesses avoid operational disruptions.
Less Downtime and Fewer Disruptions
AI-driven EDR significantly speeds up incident response, cutting response times by 50% to 70%. This improvement translates to reduced downtime, which is especially important when downtime costs small businesses an average of $8,500 per hour. Automated systems respond quickly by isolating infected devices and stopping malicious processes. This ensures that business operations can continue smoothly while threats are handled in the background, minimizing both technical and operational impacts.
Affordable Solutions for SMEs
AI-driven monitoring isn’t just about better security - it’s also a cost-effective option for small and medium-sized enterprises (SMEs). With licensing fees ranging from $30 to $100 per endpoint annually, businesses with limited budgets can access enterprise-level protection. Companies that integrate AI and automation into their security workflows save an average of $2.2 million in data breach costs compared to those that don’t. This is critical when 43% of small businesses experience cyberattacks, yet only 14% are adequately prepared. Considering data breaches can cost anywhere from $120,000 to $1.24 million, and 40% to 60% of affected small businesses close within six months, the stakes are high. By automating security tasks, smaller IT teams can manage more devices without needing highly specialized staff, making top-tier protection both accessible and essential for avoiding potentially devastating financial losses.
How to Choose the Right Tool
Evaluate Key Criteria
Picking the right AI endpoint tool comes down to aligning its features with your team's expertise and your business objectives. For small and medium-sized businesses, tools with user-friendly dashboards and extensive automation should be at the top of your list. For example, SentinelOne offers a "set-and-forget" approach, ideal for teams with limited technical know-how.
Look for platforms that provide autonomous threat detection, isolation, and remediation. These systems dramatically reduce Mean Time to Respond (MTTR), with 61.2% of AI users reporting faster threat responses. Additionally, prioritize solutions offering one-click ransomware rollback, which allows encrypted files to be restored instantly.
Another key feature to consider is AI-driven alert consolidation. Tools that rank alerts by their criticality can save time and reduce noise. Take advantage of free trials to test the tool’s interface and evaluate how well it minimizes unnecessary alerts. Also, ensure the agent is lightweight, consuming less than 5% of CPU and memory, to avoid slowing down your systems.
Make sure the tool supports multiple operating systems, including Windows, macOS, Linux, and mobile platforms. It should also integrate with software like Microsoft 365, SIEM, or SOAR systems. If you’re working with older hardware, check for legacy support. Finally, opt for a solution that can scale easily, allowing you to add endpoints without requiring major adjustments.
Comparison Table of Leading Tools
Here’s a quick comparison of top tools based on the criteria mentioned above:
| Feature | SentinelOne Singularity | Acronis Cyber Protect | Trend Micro Vision One |
|---|---|---|---|
| Best For | SMBs needing autonomous security | Businesses prioritizing backup & security | Large enterprises needing XDR visibility |
| AI Capability | Behavioral AI with "Storyline" mapping | Tunable machine learning with unified agent | AI-powered XDR across multiple layers |
| Response | One-click ransomware rollback | Disaster recovery with automated isolation | Custom playbooks and virtual patching |
| Ease of Use | High; single-pane-of-glass view | High; lightweight agent (<5% CPU) | Moderate; unified dashboard for hybrid teams |
| Platform Support | Windows, macOS, Linux, Cloud | Windows, macOS, Linux, Mobile | Windows, macOS, Linux |
| Pricing | Starts at $79.99/endpoint/year | Starts at $199.49/year for 10 devices | Enterprise pricing (contact vendor) |
| Detection Accuracy | 100% protection rate in AVLabs test | 95% recommendation rate on G2 | 90%+ detection accuracy |
This table highlights essential factors like AI capabilities, ease of use, platform support, and pricing, making it easier to identify which tool fits your needs.
AI Endpoint Monitoring Trends in 2026
Predictive Analytics Growth
By 2026, endpoint security has evolved from being reactive to taking a proactive stance. Predictive analytics now plays a critical role in identifying early warning signs of cyberattacks, stopping threats before they cause harm. For instance, modern systems can detect pre-encryption signals from ransomware, enabling them to block the attack before files are locked.
These advancements build on traditional detection methods by correlating activity across multiple devices. This approach allows AI to spot lateral movements that might go unnoticed by individual sensors. The result? Real-time containment in just seconds, significantly reducing the potential damage. With businesses prioritizing such forward-thinking defenses, the global endpoint security market is expected to surpass $13 billion.
"Resilience is no longer a passive goal. Businesses need modern, unified cybersecurity foundations that help them eliminate vulnerabilities before they're exploited, stop active threats at machine speed, and recover quickly."
– Mike Adler, Chief Technology and Product Officer, N-able
Today's monitoring systems also provide more precise control over AI agents. Instead of blocking entire applications, they now manage specific actions - like allowing file reading while preventing code generation. This level of detail is increasingly vital as AI becomes more embedded in operating systems like Windows 11, requiring security tools to oversee local AI processes that bypass traditional network traffic.
As these proactive capabilities grow, small and medium-sized enterprises (SMEs) are increasingly embracing AI technologies to enhance their cybersecurity posture.
More SMEs Adopting AI
Advanced predictive analytics have become a game-changer for SMEs, helping them address the cybersecurity skills gap. By 2026, average cybersecurity spending per employee is expected to reach $4.59. AI serves as a force multiplier, enabling small teams to efficiently manage thousands of devices without adding more staff.
The urgency for SMEs to adopt AI-powered tools is heightened by the rise of AI-driven cyberattacks. For example, 62% of mid-market organizations report an increase in AI-enabled phishing and deepfake scams. Threat actors now use tools like WormGPT to create polymorphic malware that constantly rewrites itself, making traditional defenses ineffective. Behavioral analysis has become the only reliable way to counter these threats. By deploying AI-native security solutions, SMEs can now access the same advanced protections that larger enterprises rely on.
These tools also align perfectly with the needs of hybrid and remote work setups. AI-powered security focuses on device-level behavioral analysis rather than just monitoring network traffic, ensuring protection for devices operating outside traditional network perimeters. This shift is reflected in the fact that 67% of AI investments are now directed toward integrating these tools into core business operations.
Conclusion and Key Takeaways
AI-powered endpoint monitoring has become a must-have for SMEs in 2026. Traditional antivirus systems, which rely on signature-based detection, fail to catch 44% of modern attacks. Why? Because they can't identify zero-day threats or attacks that exploit legitimate system tools, like "living-off-the-land" techniques. With the average cost of a breach hitting $3.3 million per incident, relying on outdated defenses is a risk most businesses can't afford.
AI changes the game by focusing on behavior rather than static signatures. It can detect and neutralize threats in milliseconds - an essential feature in a world where 40% of organizations now operate in hybrid work environments. With employees connecting from home offices and coffee shops, traditional network perimeters are no longer sufficient. This shift highlights the importance of proactive, AI-driven monitoring tools.
"IT stakeholders can no longer say that their protection is sufficient if they are relying solely on traditional endpoint security solutions that do not implement AI and machine learning." – NinjaOne
Beyond bolstering security, AI-powered monitoring simplifies operations for small IT teams. It cuts false positive alerts by 90%, freeing up teams to focus on real threats without constant manual oversight. Businesses using AI-enhanced protection report up to 40% greater cost efficiency compared to traditional methods, with many achieving a 300% return on investment in under 18 months.
When choosing a solution, prioritize tools that emphasize speed, visibility, and ease of deployment over unnecessary complexity. Test options in a controlled environment before rolling them out organization-wide. With costs ranging from $15 to $50 per endpoint per month, this investment is both manageable and critical to safeguarding your business.
FAQs
How long does AI endpoint monitoring take to learn normal behavior?
AI endpoint monitoring typically requires anywhere from several days to a few weeks to fully understand what constitutes normal behavior. The time it takes varies based on factors such as the specific platform in use and the complexity of the environment being observed.
Will AI monitoring slow down my laptops or servers?
When done correctly, AI monitoring usually doesn’t cause laptops or servers to lag. Today’s endpoint sensors and agents are built for real-time operation, ensuring they have little to no effect on system performance.
What should I deploy first for a small business rollout?
Start by taking a close look at your current setup to figure out where your security might be falling short. Here’s how to approach it:
- Evaluate your existing endpoint security: Identify any vulnerabilities or gaps that could leave your system exposed. This step helps you understand where improvements are most needed.
- Set a budget and prioritize: Focus on measures that will have the biggest impact first. Allocating resources effectively can make a significant difference.
- Implement AI-powered tools gradually: Start with areas that are most at risk, and roll out new tools in phases. This approach allows for smoother integration and better resource management.
By following this plan, you can strengthen your security in a way that’s both strategic and efficient, without overburdening your budget or team.


